Join Lisa Bock for an in-depth discussion in this video, Using Wireshark to crack WEP, part of Learning Cryptography and Network Security. Tom's Guide is supported by its audience. When you purchase through links on our site, we may earn an affiliate commission. News; How To Crack WEP - Part 1: Setup & Network Recon.
Even if you know you need to secure your Wi-Fi network (and have already done so), you probably find all the security protocol acronyms a little bit puzzling. Read on as we highlight the differences between protocols like WEP, WPA, and WPA2—and why it matters which acronym you slap on your home Wi-Fi network.
What Does It Matter?
You did what you were told to do, you logged into your router after you purchased it and plugged it in for the first time, and set a password. What does it matter what the little acronym next to the security protocol you chose was? As it turns out, it matters a whole lot. As is the case with all security standards, increasing computer power and exposed vulnerabilities have rendered older Wi-Fi standards at risk. It’s your network, it’s your data, and if someone hijacks your network for their illegal hijinks, it’ll be your door the police come knocking on. Understanding the differences between security protocols and implementing the most advanced one your router can support (or upgrading it if it can’t support current gen secure standards) is the difference between offering someone easy access to your home network and not.
WEP, WPA, and WPA2: Wi-Fi Security Through the Ages
Since the late 1990s, Wi-Fi security protocols have undergone multiple upgrades, with outright deprecation of older protocols and significant revision to newer protocols. A stroll through the history of Wi-Fi security serves to highlight both what’s out there right now and why you should avoid older standards.
Wired Equivalent Privacy (WEP)
Wired Equivalent Privacy (WEP) is the most widely used Wi-Fi security protocol in the world. This is a function of age, backwards compatibility, and the fact that it appears first in the protocol selection menus in many router control panels.
WEP was ratified as a Wi-Fi security standard in September of 1999. The first versions of WEP weren’t particularly strong, even for the time they were released, because U.S. restrictions on the export of various cryptographic technology led to manufacturers restricting their devices to only 64-bit encryption. When the restrictions were lifted, it was increased to 128-bit. Despite the introduction of 256-bit WEP, 128-bit remains one of the most common implementations.
Despite revisions to the protocol and an increased key size, over time numerous security flaws were discovered in the WEP standard. As computing power increased, it became easier and easier to exploit those flaws. As early as 2001, proof-of-concept exploits were floating around, and by 2005, the FBI gave a public demonstration (in an effort to increase awareness of WEP’s weaknesses) where they cracked WEP passwords in minutes using freely available software.
CANON DISCLAIMS ALL WARRANTIES, EXPRESS OR IMPLIED, INCLUDING, WITHOUT LIMITATION, IMPLIED WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NON-INFRINGEMENT.CANON U.S.A.,Inc. DISCLAIMERCANON U.S.A.,Inc. Canon toolbox download windows 10. MAKES NO GUARANTEES OF ANY KIND WITH REGARD TO ANY PROGRAMS, FILES, DRIVERS OR ANY OTHER MATERIALS CONTAINED ON OR DOWNLOADED FROM THIS, OR ANY OTHER, CANON SOFTWARE SITE. ALL SUCH PROGRAMS, FILES, DRIVERS AND OTHER MATERIALS ARE SUPPLIED 'AS IS.'
Despite various improvements, work-arounds, and other attempts to shore up the WEP system, it remains highly vulnerable. Systems that rely on WEP should be upgraded or, if security upgrades are not an option, replaced. The Wi-Fi Alliance officially retired WEP in 2004.
Wi-Fi Protected Access (WPA)
Wi-Fi Protected Access (WPA) was the Wi-Fi Alliance’s direct response and replacement to the increasingly apparent vulnerabilities of the WEP standard. WPA was formally adopted in 2003, a year before WEP was officially retired. The most common WPA configuration is WPA-PSK (Pre-Shared Key). The keys used by WPA are 256-bit, a significant increase over the 64-bit and 128-bit keys used in the WEP system.
Some of the significant changes implemented with WPA included message integrity checks (to determine if an attacker had captured or altered packets passed between the access point and client) and the Temporal Key Integrity Protocol (TKIP). TKIP employs a per-packet key system that was radically more secure than the fixed key system used by WEP. The TKIP encryption standard was later superseded by Advanced Encryption Standard (AES).
Despite what a significant improvement WPA was over WEP, the ghost of WEP haunted WPA. TKIP, a core component of WPA, was designed to be easily rolled out via firmware upgrades onto existing WEP-enabled devices. As such, it had to recycle certain elements used in the WEP system which, ultimately, were also exploited.
WPA, like its predecessor WEP, has been shown via both proof-of-concept and applied public demonstrations to be vulnerable to intrusion. Interestingly, the process by which WPA is usually breached is not a direct attack on the WPA protocol (although such attacks have been successfully demonstrated), but by attacks on a supplementary system that was rolled out with WPA—Wi-Fi Protected Setup (WPS)—which was designed to make it easy to link devices to modern access points.
Wi-Fi Protected Access II (WPA2)
WPA has, as of 2006, been officially superseded by WPA2. One of the most significant changes between WPA and WPA2 is the mandatory use of AES algorithms and the introduction of CCMP (Counter Cipher Mode with Block Chaining Message Authentication Code Protocol) as a replacement for TKIP. https://golkk.netlify.app/iso-for-virtualbox.html. However, TKIP is still preserved in WPA2 as a fallback system and for interoperability with WPA.
4 minutes to read; In this article. XInput is an API that allows applications to receive input from the Xbox Controller for Windows. This document describes the differences between XInput and DirectInput implementations of the Xbox Controller and how you can support XInput devices and legacy DirectInput devices at the same time. Input Mapper is designed to bridge the gap between the devices you use and the games you play. Started in 2014 as DS4Tool and then DS4Windows, Input Mapper immediately gained a strong following after allowing users to use their Dualshock 4 controllers in games that don't allow for the direct input protocol used by the device. Starting in 2015 the project began to seek beyond just Dualshock 4. Controller mapper windows 10. Aug 23, 2015 How to Fix Input Mapper on Windows 10 August 23, 2015. Kevin shows just how easy it is to get Input Mapper and Windows 10 working with a DS4, and any game that requires exclusive mode.
Currently, the primary security vulnerability to the actual WPA2 system is an obscure one (and requires the attacker to already have access to the secured Wi-Fi network in order to gain access to certain keys and then perpetuate an attack against other devices on the network). As such, the security implications of the known WPA2 vulnerabilities are limited almost entirely to enterprise level networks and deserve little to no practical consideration in regard to home network security.
Unfortunately, the same vulnerability that is the biggest hole in the WPA armor—the attack vector through the Wi-Fi Protected Setup (WPS)—remains in modern WPA2-capable access points. Although breaking into a WPA/WPA2 secured network using this vulnerability requires anywhere from 2-14 hours of sustained effort with a modern computer, it is still a legitimate security concern. WPS should be disabled and, if possible, the firmware of the access point should be flashed to a distribution that doesn’t even support WPS so the attack vector is entirely removed.
Wi-Fi Security History Acquired; Now What?
At this point, you’re either feeling a little smug (because you’re confidently using the best security protocol available for your Wi-Fi access point) or a little nervous (because you picked WEP since it was at the top of the list). If you’re in the latter camp, don’t fret; we have you covered.
Before we hit you with a further-reading list of our top Wi-Fi security articles, here’s the crash course. This is a basic list ranking the current Wi-Fi security methods available on any modern (post-2006) router, ordered from best to worst:
- WPA2 + AES
- WPA + AES
- WPA + TKIP/AES (TKIP is there as a fallback method)
- WPA + TKIP
- WEP
- Open Network (no security at all)
Ideally, you’ll disable Wi-Fi Protected Setup (WPS) and set your router to WPA2 + AES. Everything else on the list is a less than ideal step down from that. Once you get to WEP, your security level is so low, it’s about as effective as a chain link fence—the fence exists simply to say “hey, this is my property” but anyone who actually wanted in could just climb right over it.
If all this thinking about Wi-Fi security and encryption has you curious about other tricks and techniques you can easily deploy to further secure your Wi-Fi network, your next stop should be browsing the following How-To Geek articles:
Armed with a basic understanding of how Wi-Fi security works and how you can further enhance and upgrade your home network access point, you’ll be sitting pretty with a now secure Wi-Fi network.
READ NEXT- › How to Use Text Editing Gestures on Your iPhone and iPad
- › Windows 10’s BitLocker Encryption No Longer Trusts Your SSD
- › How to Disable or Enable Tap to Click on a PC’s Touchpad
- › How HTTP/3 and QUIC Will Speed Up Your Web Browsing
- › Motherboards Explained: What Are ATX, MicroATX, and Mini-ITX?
You already know that if you want to lock down your Wi-Fi network, you should opt for WPA encryption because WEP is easy to crack. But did you know how easy? Take a look.
Secure Your Home Wi-Fi Network
Tech site Ars Technica runs down the basics of securing your home wireless network with the most…
Read more ReadAdvertisement
Note: This post demonstrates how to crack WEP passwords, an older and less often used network security protocol. If the network you want to crack is using the more popular WPA encryption, see our guide to cracking a Wi-Fi network's WPA password with Reaver instead.
How to Crack a Wi-Fi Network's WPA Password with Reaver

Your Wi-Fi network is your conveniently wireless gateway to the internet, and since you're not …
Read more ReadToday we're going to run down, step-by-step, how to crack a Wi-Fi network with WEP security turned on. But first, a word: Knowledge is power, but power doesn't mean you should be a jerk, or do anything illegal. Knowing how to pick a lock doesn't make you a thief. Consider this post educational, or a proof-of-concept intellectual exercise.
How to Pick a Lock with a Bump Key
From the 'use this for good, not evil' files comes a fascinating instructional video on…
Read more ReadAdvertisement
Dozens of tutorials on how to crack WEP are already all over the internet using this method. Seriously—Google it. This ain't what you'd call 'news.' But what is surprising is that someone like me, with minimal networking experience, can get this done with free software and a cheap Wi-Fi adapter. Here's how it goes.
What You'll Need
Unless you're a computer security and networking ninja, chances are you don't have all the tools on hand to get this job done. Here's what you'll need:
- A compatible wireless adapter—This is the biggest requirement. You'll need a wireless adapter that's capable of packet injection, and chances are the one in your computer is not. After consulting with my friendly neighborhood security expert, I purchased an Alfa AWUS050NH USB adapter, pictured here, and it set me back about $50 on Amazon. Update: Don't do what I did. Get the Alfa AWUS036H, not the US050NH, instead.The guy in this video below is using a $12 model he bought on Ebay (and is even selling his router of choice). There are plenty of resources on getting aircrack-compatible adapters out there.
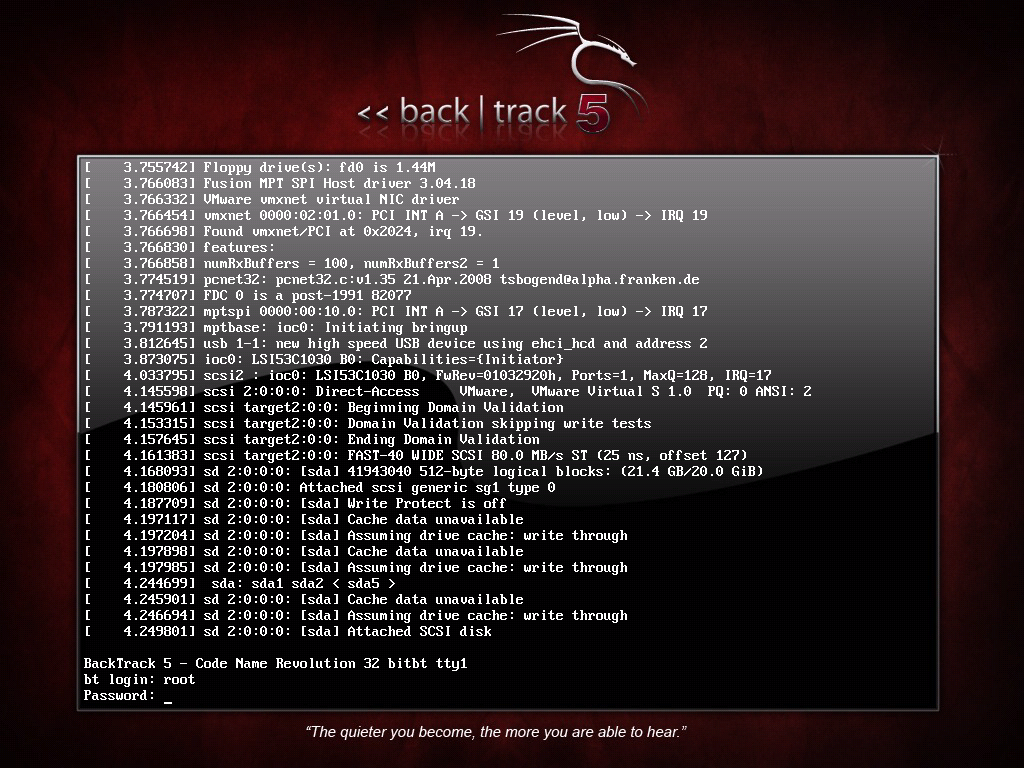
- A BackTrack Live CD. We already took you on a full screenshot tour of how to install and use BackTrack 3, the Linux Live CD that lets you do all sorts of security testing and tasks. Download yourself a copy of the CD and burn it, or load it up in VMware to get started.
- A nearby WEP-enabled Wi-Fi network. The signal should be strong and ideally people are using it, connecting and disconnecting their devices from it. The more use it gets while you collect the data you need to run your crack, the better your chances of success.
- Patience with the command line. This is an ten-step process that requires typing in long, arcane commands and waiting around for your Wi-Fi card to collect data in order to crack the password. Like the doctor said to the short person, be a little patient.
Advertisement
Crack That WEP
To crack WEP, you'll need to launch Konsole, BackTrack's built-in command line. It's right there on the taskbar in the lower left corner, second button to the right. Now, the commands.
Advertisement
First run the following to get a list of your network interfaces:
The only one I've got there is labeled ra0. Yours may be different; take note of the label and write it down. From here on in, substitute it in everywhere a command includes (interface).
How To Crack Wep Encryption
Advertisement
Now, run the following four commands. See the output that I got for them in the screenshot below.
Advertisement
If you don't get the same results from these commands as pictured here, most likely your network adapter won't work with this particular crack. If you do, you've successfully 'faked' a new MAC address on your network interface, 00:11:22:33:44:55.
Advertisement
Now it's time to pick your network. Run:
To see a list of wireless networks around you. When you see the one you want, hit Ctrl+C to stop the list. Highlight the row pertaining to the network of interest, and take note of two things: its BSSID and its channel (in the column labeled CH), as pictured below. Obviously the network you want to crack should have WEP encryption (in the ENC) column, not WPA or anything else.
Advertisement
Like I said, hit Ctrl+C to stop this listing. (I had to do this once or twice to find the network I was looking for.) Once you've got it, highlight the BSSID and copy it to your clipboard for reuse in the upcoming commands.
Advertisement
Now we're going to watch what's going on with that network you chose and capture that information to a file. Run:
Where (channel) is your network's channel, and (bssid) is the BSSID you just copied to clipboard. Veeam one free edition. You can use the Shift+Insert key combination to paste it into the command. Enter anything descriptive for (file name). I chose 'yoyo,' which is the network's name I'm cracking.
Advertisement
You'll get output like what's in the window in the background pictured below. Leave that one be. Open a new Konsole window in the foreground, and enter this command:
Here the ESSID is the access point's SSID name, which in my case is yoyo. What you want to get after this command is the reassuring 'Association successful' message with that smiley face.
Advertisement
You're almost there. Now it's time for:
Here we're creating router traffic to capture more throughput faster to speed up our crack. After a few minutes, that front window will start going crazy with read/write packets. (Also, I was unable to surf the web with the yoyo network on a separate computer while this was going on.) Here's the part where you might have to grab yourself a cup of coffee or take a walk. Basically you want to wait until enough data has been collected to run your crack. Watch the number in the '#Data' column—you want it to go above 10,000. (Pictured below it's only at 854.)
Advertisement
Depending on the power of your network (mine is inexplicably low at -32 in that screenshot, even though the yoyo AP was in the same room as my adapter), this process could take some time. Wait until that #Data goes over 10k, though—because the crack won't work if it doesn't. In fact, you may need more than 10k, though that seems to be a working threshold for many.
Free computer graphics software. You can use Canva in the browser for the full experience, but most tools are available for both Android and iOS. Of particular note is the ability to trace bitmap images, support for variable width strokes and native import of Illustrator files. Edit images, create colour palettes, match font pairs and more with Canva. Platform: Browser, iOS, Android.It seems harsh to place Canva under the 'Image Editing Software' heading because it does so much more. Canva is a photo editor, colour palette tool, font combination picker, learning resource, and photo collage maker, and it even features a dedicated with hundreds of free design elements and fonts at your fingertips.It's really more of a full graphic design suite than a photo editor, and while it comes some way short of offering the breadth of abilities of Adobe Creative Cloud, its simplicity, variety of useful tools, and inspirational learning assets make Canva a hit.
Advertisement
Once you've collected enough data, it's the moment of truth. Launch a third Konsole window and run the following to crack that data you've collected:
Here the filename should be whatever you entered above for (file name). You can browse to your Home directory to see it; it's the one with .cap as the extension.
Break Wep Encryption
Advertisement
If you didn't get enough data, aircrack will fail and tell you to try again with more. If it succeeds, it will look like this:
Advertisement
The WEP key appears next to 'KEY FOUND.' Drop the colons and enter it to log onto the network.
Problems Along the Way
With this article I set out to prove that cracking WEP is a relatively 'easy' process for someone determined and willing to get the hardware and software going. I still think that's true, but unlike the guy in the video below, I had several difficulties along the way. In fact, you'll notice that the last screenshot up there doesn't look like the others—it's because it's not mine. Even though the AP which I was cracking was my own and in the same room as my Alfa, the power reading on the signal was always around -30, and so the data collection was very slow, and BackTrack would consistently crash before it was complete. After about half a dozen attempts (and trying BackTrack on both my Mac and PC, as a live CD and a virtual machine), I still haven't captured enough data for aircrack to decrypt the key.
Advertisement
So while this process is easy in theory, your mileage may vary depending on your hardware, proximity to the AP point, and the way the planets are aligned. Oh yeah, and if you're on deadline—Murphy's Law almost guarantees it won't work if you're on deadline.
Got any experience with the WEP cracking courtesy of BackTrack? What do you have to say about it? Give it up in the comments.
Advertisement